Psycotrace
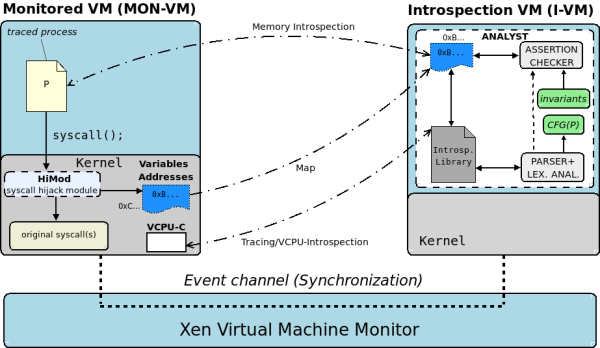
PsycoTrace is a virtualization-based monitoring system that protects a process P from attacks that alter the process self as specified by the program source code. P self is described by traces of system calls and invariants paired with invocations. The traces are described by a context-free grammar computed by a static analysis of the code of P. At run-time, PsycoTrace pauses and resumes P execution each time P invokes a system call to check that the trace of the calls it issues is coherent with the grammar. To increase the robustness of the monitoring system, PsycoTrace relies on two virtual machines, the monitored and the monitoring ones that, respectively, run P and the monitoring system. In this way, the machine that applies the security checks is strongly separated from the monitored one.
This is the source code for the hijacking module (HiMod, by Francesco Tamberi), and this is the source code for the Analyst (parser and Introspection Library, by Dario Maggiari), a test process and an exploit for it. Finally, Syscall Checker Analysis Tool (joint work with Carlo Casta, Marco Fais, Michele Onnis and Dario Maggiari) includes cparser, which processes .c files to generate an AST in xml format that can then be processed by ast2grammar to generate a scanner and a parser for the system call grammar. All the programs have been tested on Xen 3.1.0 (compiled from source code) with Linux kernel 2.6.18-xen (both on domain 0 and domain U).
This is the full listing of the Himod:
reader.c writer.c
This is the full listing of the Analyst:
gen_grammar_nflex.sh grammar-test.y reader.c README tv_checker.c tv_mm_intros_fun.c tv_mm_intros_fun.h tv_page_macro.h domu/trova-ind.c domu/daemon-exp.c domu/daemon.c domu/README


